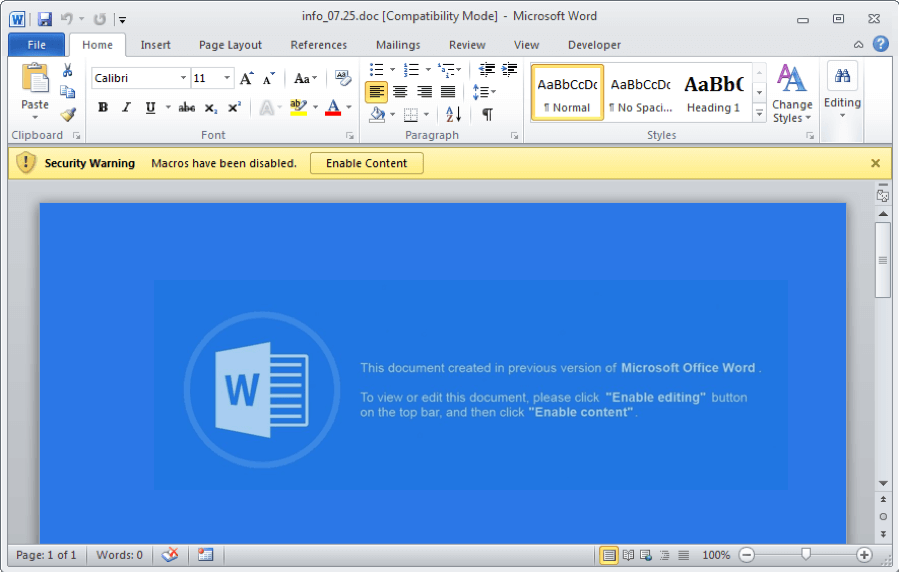
Magniber ransomware is spreading like wildfire thanks to a coordinated effort that began in early April and involves the exploitation of bogus Windows 10 patches.
What is ransomware?
In the simplest words, ransomware is a type of malware that affects your computer and demands a ransom in exchange for access to it. It encrypts all of your files and directs you to contact the hacker in order to negotiate a payment arrangement. As a result, we have RANSOMware!
According to BleepingComputer, “Based on the submissions to VirusTotal, this campaign appears to have started on April 8th, 2022 and has seen massive distribution worldwide since then. While it’s not 100% clear how the fake Windows 10 updates are being promoted, the downloads are distributed from fake warez and crack sites.”
This particular exploit targeted consumers instead of companies.
To avoid any and all unwanted cyber assaults, make sure that your antivirus software is current on your computer. Keep in mind that Windows 10 and 11 updates are sent through the operating system. Microsoft will never send updates through other channels such as e-mail or social media.
If you ever have an issue with any Windows 10 updates, give us a call at 1-800-620-5285. Karls Technology is a nationwide computer service company with offices in many major cities. This blog article was written by a member of our team at the Garland Computer Repair Service. If you need computer repair in Garland, TX please call or text the local office at (469) 299-9005.