In short, yes. Many people assume it’s only your computer. However, through fraudulent messaging clients, hackers can access data, location, photos and more from your personal or business mobile phones, invading your privacy. And there are a handful of ways they can get sneaky.
According to EFF.org, “The trojanized apps, including Signal and WhatsApp, function like the legitimate apps and send and receive messages normally. However, the fake apps also allow the attackers to take photos, retrieve location information, capture audio, and more.” (source: https://www.eff.org/press/releases/eff-and-lookout-uncover-new-malware-espionage-campaign-infecting-thousands-around)
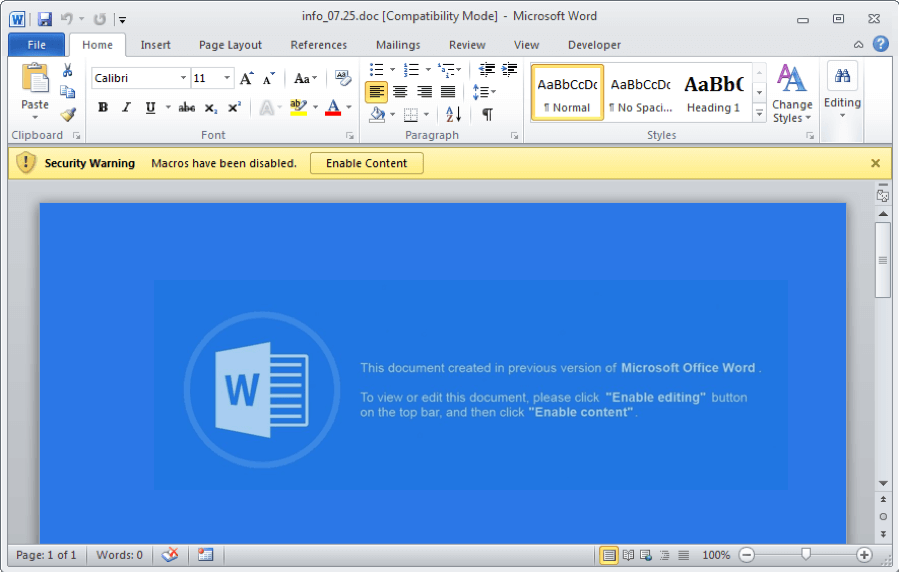
Along with fake apps, you can also receive text messages, e-mails, and instant messages with web links from an unknown source. This technique is called phishing messages and can allow hackers to acquire any login information you may have saved on your phone.
If you notice an open WIFI when choosing a network, you might also be at risk of your phone being hacked. Unsecured WIFI networks can sometimes have snoopers behind the scenes, waiting for users to join and surf the web or log in to highly sensitive (or personal) accounts. This gives them ample opportunity to steal anything they want. Keep an eye out for URLs with unsecured vs secured connections (http: VS https:).
You can protect yourself from these, and other possible risks, by creating strong passwords, using two-factor authentication and setting up security questions for your passwords. Be sure to play it safe with any and all personal information you add to your phone.